Agentless Monitoring Solutions
Fast and flexible, unified IT monitoring: servers, applications, network, storage, virtualization and cloud
Free TrialWhat is Agentless Monitoring?
Monitoring IT infrastructures often involves the installation of agent software on target servers to collect performance metrics about the servers and application servers executing on them. Performance metrics collected by the agents are then uploaded to a management server for storage, analysis, alerting and reporting to administrators. The need to install and maintain agent software on all monitored servers is a key drawback with this approach.
Agentless monitoring, on the other hand, collects performance metrics from the infrastructure without installing any agent software on the servers or devices being monitored – which makes the agentless approach easier to manage than agent-based monitoring.

I like eG Enterprise's ability to monitor just about every component you can think of in our entire organization, and be able to show it on one single dashboard. It's really an excellent product.![]()
When to use
Agentless Monitoring?
Agentless monitoring is suitable to monitor many IT infrastructure components. Without having to install and manage an agent, various parts of the infrastructure can be monitored and performance metrics obtained in an agentless manner. Whether one wants to use a monitoring agent or go the agentless route is completely based on their organizational policy requirements and custom needs. Given below is a list of IT infrastructure components that are recommended to be monitored in an agentless manner:
Agentless Monitoring with
eG Enterprise
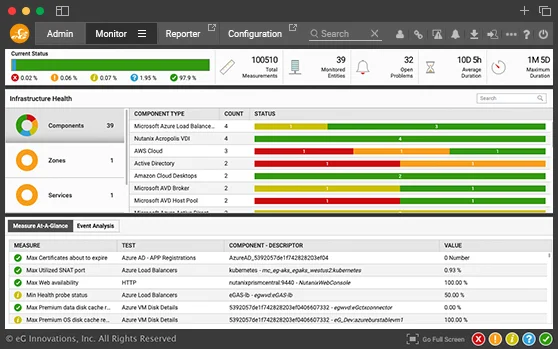
eG Enterprise supports both agentless and agent-based monitoring. Administrators can choose which parts of the infrastructure they want to monitor agentlessly, and which components to monitor using agents.
In eG Enterprise, agentless monitoring is implemented using a remote data collector that uses protocols such as SSH for Unix monitoring, Windows management instrumentation (WMI) for Windows servers and applications, HTTP/S for web-based applications, JMX for Java applications, SNMP for network devices, etc.

Agentless monitoring is recommended for network devices and storage devices, as well as for virtualization and virtual desktop monitoring where strong APIs are supported by the underlying platforms. For application servers running on legacy operating systems like Windows and Linux, agent-based monitoring is usually preferred. View supported platforms and technologies »
Infrastructure-Wide Performance Correlation
and Automatic Root Cause Diagnosis
eG Enterprise dissects the processing time of web transactions and identifies what is causing slowdown.
Agentless Monitoring with
eG Enterprise
While the following examples illustrate the versatility of agentless monitoring solutions like eG Enterprise, it is important to note that these concepts can be applied across various industries and verticals. The flexibility and effectiveness of agentless monitoring make it an invaluable tool for addressing diverse business challenges.
Use Cases: Agentless Monitoring in Action
eG Enterprise agentless monitoring caters to versatile use cases, customized for varying business goals. It allows users to leverage the tool for tackling challenges pertaining to their specific needs, ensuring significant improvements over time.
Here are some use cases highlighting how agentless monitoring can be instrumental in saving time and effort for the IT team.
Examples:
Frequent Application Slowdowns
For instance, large hospital networks face frequent application slowdowns, impacting patient care delivery. The use of traditional monitoring further restricts visibility into the underlying infrastructure, causing performance issues.
Solution: eG Enterprise provides real-time insights into network performance, server health, and application responsiveness, as exemplified in the hospital scenario. This enables the identification of bottlenecks and root causes of slowdowns in no time, leading to significant improvements in application responsiveness.
Server Outage During Website Traffic Spikes
Similarly, major online retailers often struggle with high website traffic spikes during peak shopping seasons. Eventually, this leads to outages and lost sales opportunities.
Solution: eG Enterprise’s capability to track website performance metrics ensures an enhanced user experience during peak traffic periods. This proactive approach optimizes infrastructure and application performance, minimizing downtime and maximizing revenue.
Equipment Failure Leading to Production Line Disruption
In manufacturing companies, unexpected equipment failures lead to frequent production line disruptions. The major reason is the lack of visibility into critical industrial equipment health and performance.
Solution: eG Enterprise enables sensor data tracking from machineries, allowing real-time monitoring of key performance indicators (KPIs) like temperature, humidity, and energy consumption.
This proactive identification of potential equipment failure enables scheduling preventive maintenance to minimize downtime, applicable across various manufacturing sectors.
Compliance Challenges
Compliance challenges are predominant within financial institutions due to the lack of insights into user activity and application access within their IT infrastructure.
Solution: eG Enterprise tracks user activity logs and application access across financial institutions’ networks, providing a comprehensive audit trail for compliance purposes. This real-time insight ensures adherence to regulatory compliance requirements. It is also applicable to various other industries with stringent compliance needs.
Empower Smarter Decisions:
Choose the eG Enterprise Agentless Monitoring Solution
These examples highlight the versatility and effectiveness of agentless monitoring tools and showcase a powerful way to gain real-time visibility into IT infrastructure, simplifying management and optimizing performance across diverse industries. Whether addressing application performance, server uptime, equipment health, or compliance challenges, the proactive capabilities of agentless monitoring empower smarter decisions and ensure seamless operations.
Here are a few considerations and reasons why you must choose eG Enterprise:
Comparing Agentless and Agent-based Monitoring
| Agentless Monitoring | Agent-based Monitoring | |
|---|---|---|
| Ease of deployment | Easier to deploy. Software installation is required only on the remote data collector. | Agent deployment is required on each server. |
| Security | The remote data collector must be allowed to communicate with the target system on different ports. The data collector may also need to be installed with domain administration privileges in order to access the remote systems. | Much more secure than agentless monitoring. The agent to application/OS communications are handled internal to the server. Hence, no additional firewall rules need to be configured. |
| Network overhead | Introduces additional network traffic as the raw performance data is transported to a remote data collector. | Bandwidth efficient: Data is collected locally and only the processed results are transported to the console. |
| Breadth and depth of monitoring | Can be limited because not all applications and systems have built-in monitoring capabilities. | Provides deeper, broader monitoring. |