Comprehensive, Out-Of-The-Box
Alerting and Reporting for Azure AD
eG Enterprise proactively and continuously collects, and monitors data associated with Azure AD metrics, events, log and traces. Simplifying and automating tasks such as:

- Actively monitoring successful and failed logons and alerting on suspicious behaviors
- Monitoring app registrations and their RBAC roles and permissions
- Tracking secret and certificate errors and expiration warnings
- Auditing activities such as adding, deleting and modifying users, applications, service principals, groups, policies, members, etc.
- Monitoring and auditing different sign-in logs
- Monitoring users and their last login date and time, stale users & devices.
Ensure Security and Compliance
- Maintain a comprehensive audit trail of activities to meet your SOX, PCI DSS, HIPAA, GDPR, GLBA and FISMA requirements.
- ITSM service and help desk tool integrations with all major vendors including ServiceNow, Autotask, JIRA and others; to ensure actions arising are processed within standard and traceable processes as needed.
- Additional alerting options include SMS, email, Slack, WhatsApp, in-browser notifications and the secure eG Enterprise mobile apps for iOS and Android. Rapid notification in the event of attempted security breaches.
- Store Azure AD audit data for as long as it is needed to meet compliance demands and regulations.
- A secure platform architecture including granular Role Based Access (RBAC) control to ensure secure and restricted access to your data and built-in enterprise grade audit reporting for those needing to meet regulatory compliance requirements.
- 24x7, follow-the-sun support enterprise options serviced by 12 regional offices worldwide supporting 8 native languages ensure you can rely on eG Innovations.
Full Coverage of
Azure AD Connect and
On-premises Active Directory
eG Enterprise covers the full range of Azure AD usage scenarios, whether that is standalone or in conjunction with Azure AD Connect and on-premises Active Directory components. A single pane of glass for your whole logon and authentication process.
Synchronization task failures and connectivity issues that mean users are unable to access the resources are proactively checked for. Administrators have full insights to rectify problems before end users report issues accessing resources.
Integration with eG Enterprise’s comprehensive support for Active Directory allows a unified view of authentication across hybrid infrastructures beyond Azure.
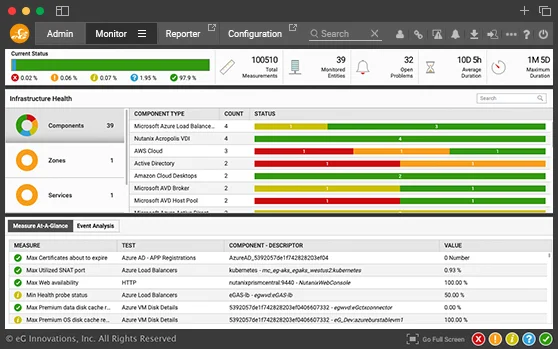
User Activity Monitoring
eG Enterprise’s Azure Active Directory monitoring answers all the common questions about Azure AD users out of the box without having to write any KQL queries. Dashboards can be accessed out of the box or created with just a few clicks without having to rely on public domain workbooks.
Besides continually monitoring logs, metrics, and error messages, eG Enterprise also automatically performs deeper diagnostic tests, if issues exist. For example, if inactive users are detected or failed logins occur, details on those users or reasons for failure are collected and analyzed.
Coupled with automated static and dynamic thresholds, anomalies, and unusual events automatically trigger notifications that pinpoint the underlying root cause of the problem.
| Instant access to critical information on user activities allows the Azure administrator to instantly answer questions on Azure AD users, such as: |
||
|---|---|---|
Simple GUI access to Azure AD Audit logs
eG Enterprise Azure AD monitoring monitors Audit log and proactively alerts upon audit failures. All audit log records are stored in the eG database. So, you can store this data for a longer period than the Azure default for security, compliance or troubleshooting reasons.
eG Enterprise allows you to slice and dice this data without writing any KQL (Kusto Query Language) queries and without the need to import the workbooks from community repositories using custom reports and dashboards.
eG Enterprise’s Azure AD Audit log monitoring helps you to find answers for questions such as:
Monitor Azure AD Sign-in logs and Detect Attacks Proactively
Azure AD sign-in logs is an indispensable tool for troubleshooting and investigating security-related incidents in your tenant. Proactively, and constantly monitoring sign-ins can prevent breaches, alert administrators to malicious attacks and anomalous usage patterns and enable them to reduce their vulnerability by ensuring systems are configured to allow access only to those users and services that need access using up-to-date best practice authentication mechanisms and so on.
eG Enterprise's Azure AD Sign-in log monitoring helps you to find answers to questions such as:


Frequently Asked Questions (FAQs) about Azure Active Directory Monitoring Tools
You can use Azure Monitor, which requires extensive setup and configuration, or you can use a third-party tool like eG Enterprise which is pre-configured with all the metrics and thresholds for Azure AD. Read more about how to monitor Azure AD in our blog post.
Yes
Yes
No
Yes
Yes