CBR Quality of Service Test
The Citrix Branch Repeater includes integral quality-of-service (QoS) functionality that classifies traffic by flow and application. This works with various other optimization and compression technologies to control the bandwidth used and improve the user experience.
In Citrix Repeater, a traffic-shaping engine is included to manage all the TCP or User Datagram Protocol (UDP) traffic on WAN links in the incoming as well as outgoing directions. The traffic shaper is based on bandwidth-limited fair queuing, where every connection is assigned a weighted priority based on the assigned policies. Weighted priorities are applied to the actual WAN data transferred, after compression is applied. The weighted priority is based on the Application Classifiers defined in the Service Class, and you can also apply the weighted priorities on a per-link basis.
You can use the following mechanisms to apply Quality of Service:
- Link Definition: Informs the traffic shaper which WAN link the packet is using. In a site with multiple links, each link has its own bandwidth limits and is managed independently.
- Application Classifiers: Identifies and determines the protocol or application class to which traffic belongs.
- Service Classes: Maps applications to acceleration decisions, traffic filters, and traffic-shaping policies.
- Traffic Shaping Policies: Informs the traffic shaper about weighted priority and bandwidth limits to assign to which traffic type, the application classifier.
Figure 2.2 depicts the architecture for the QoS capabilities
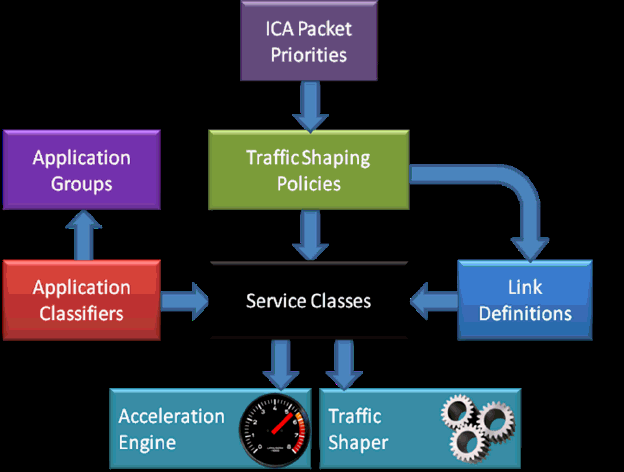
Figure 1 : The QoS architecture
If branch users complain of link slowdowns, then administrators should be able to identify which traffic-shaping policy governs traffic acceleration on that link and should figure out how to fine-tune that policy to increase link throughput. The CBR Quality of Service test helps with this! This test auto-discovers the default and user-configured traffic-shaping policies and closely observes the traffic accelerated by each policy to identify those policies that may have to be tweaked in order to improve the rate of traffic acceleration, optimize bandwidth usage, and reduce packet loss.
Target of the test : A Citrix Branch Repeater
Agent deploying the test : An external agent
Outputs of the test : One set of results for each default and user-configured traffic-shaping policy in the Citrix Branch Repeater being monitored.
| Parameter | Description |
|---|---|
|
Test Period |
How often should the test be executed. |
|
Host |
The IP address of the host for which this test is to be configured. |
|
Port |
Refers to the port at which the specified host listens to. By default, this will be NULL. |
|
SNMPPort |
The port at which the monitored target exposes its SNMP MIB; The default value is 161. |
|
SNMPVersion |
By default, the eG agent supports SNMP version 1. Accordingly, the default selection in the SNMPversion list is v1. However, if a different SNMP framework is in use in your environment, say SNMP v2 or v3, then select the corresponding option from this list. |
|
SNMPCommunity |
The SNMP community name that the test uses to communicate with the firewall. This parameter is specific to SNMP v1 and v2 only. Therefore, if the SNMPVersion chosen is v3, then this parameter will not appear. |
|
UserName |
This parameter appears only when v3 is selected as the SNMPVersion. SNMP version 3 (SNMPv3) is an extensible SNMP Framework which supplements the SNMPv2 Framework, by additionally supporting message security, access control, and remote SNMP configuration capabilities. To extract performance statistics from the MIB using the highly secure SNMP v3 protocol, the eG agent has to be configured with the required access privileges – in other words, the eG agent should connect to the MIB using the credentials of a user with access permissions to be MIB. Therefore, specify the name of such a user against this parameter. |
|
Context |
This parameter appears only when v3 is selected as the SNMPVersion. An SNMP context is a collection of management information accessible by an SNMP entity. An item of management information may exist in more than one context and an SNMP entity potentially has access to many contexts. A context is identified by the SNMPEngineID value of the entity hosting the management information (also called a contextEngineID) and a context name that identifies the specific context (also called a contextName). If the Username provided is associated with a context name, then the eG agent will be able to poll the MIB and collect metrics only if it is configured with the context name as well. In such cases therefore, specify the context name of the Username in the Context text box. By default, this parameter is set to none. |
|
AuthPass |
Specify the password that corresponds to the above-mentioned Username. This parameter once again appears only if the SNMPversion selected is v3. |
|
Confirm Password |
Confirm the AuthPass by retyping it here. |
|
AuthType |
This parameter too appears only if v3 is selected as the SNMPversion. From the AuthType list box, choose the authentication algorithm using which SNMP v3 converts the specified username and password into a 32-bit format to ensure security of SNMP transactions. You can choose between the following options:
|
|
EncryptFlag |
This flag appears only when v3 is selected as the SNMPversion. By default, the eG agent does not encrypt SNMP requests. Accordingly, the this flag is set to No by default. To ensure that SNMP requests sent by the eG agent are encrypted, select the Yes option. |
|
EncryptType |
If the EncryptFlag is set to Yes, then you will have to mention the encryption type by selecting an option from the EncryptType list. SNMP v3 supports the following encryption types:
|
|
EncryptPassword |
Specify the encryption password here. |
|
Confirm Password |
Confirm the encryption password by retyping it here. |
|
Timeout |
Specify the duration (in seconds) within which the SNMP query executed by this test should time out in this text box. The default is 10 seconds. |
|
Data Over TCP |
By default, in an IT environment, all data transmission occurs over UDP. Some environments however, may be specifically configured to offload a fraction of the data traffic – for instance, certain types of data traffic or traffic pertaining to specific components – to other protocols like TCP, so as to prevent UDP overloads. In such environments, you can instruct the eG agent to conduct the SNMP data traffic related to the monitored target over TCP (and not UDP). For this, set this flag to Yes. By default, this flag is set to No. |
|
EngineID |
This parameter appears only when v3 is selected as the SNMPVersion. Sometimes, the test may not report metrics when AES192 or AES256 is chosen as the Encryption type. To ensure that the test report metrics consistently, administrators need to set this flag to Yes. By default, this parameter is set to No. |
| Measurement | Description | Measurement Unit | Interpretation |
|---|---|---|---|
|
Data transmitted |
Indicates the rate at which data was transmitted for this traffic-shaping policy. |
KB/Sec |
At any given point in time, the value of these measures should be well-within the incoming and outgoing bandwidth usage limits set for the corresponding traffic-changing policy. If these values consistently grow towards the bandwidth usage limit, it is an indication that the traffic-shaping policy is not very effective. You may then have to fine-tune that policy to optimize bandwidth consumption. |
|
Data received |
Indicates the rate at which data was received for this traffic-shaping policy. |
KB/Sec |
|
|
Packets transmitted |
Indicates the number of packets transmitted for this traffic-shaping policy during the last measurement period. |
Number |
At any given point in time, the value of these measures should be well-within the incoming and outgoing bandwidth usage limits set for the corresponding traffic-changing policy. If these values consistently grow towards the bandwidth usage limit, it is an indication that the traffic-shaping policy is not very effective. You may then have to fine-tune that policy to optimize bandwidth consumption. |
|
Packets received |
Indicates the number of packets received for this traffic-shaping policy during the last measurement period. |
Number |
|
|
Data received before compression |
Indicates the amount of data that was received for this service class before compression, during the last measurement period. |
KB |
|
|
Data dropped during transmission: |
Indicates the rate of traffic dropped because of this traffic-shaping policy. |
KB/Sec |
A high value for these measures could indicate one of the following:
|
|
Data dropped during reception |
Indicates the rate of traffic not received due to this traffic-shaping policy. |
KB/Sec |
|
|
Packets dropped during transmission |
Indicates the number of packets dropped during transmissions due to this traffic-shaping policy. |
Number |
A high value for these measures could indicate one of the following:
|
|
Packets dropped during reception |
Indicates the number of packets not received due to this traffic-shaping policy. |
Number |