CPU - Xen Test
This test reports the real-time CPU utilization statistics pertaining to the control domain and every processor supported by the Citrix Hypervisor. The control domain is a privileged VM that provides low-level services to other VMs, such as providing access to physical devices. It also runs the management tool stack. Using this test, administrators can determine whether there is a resource-contention at the Citrix Hypervisor host, and if so, where - at the control domain? or with the processors supported by the host?
Target of the test : A Citrix Hypervisor host
Agent deploying the test : An internal/remote agent
Outputs of the test : One set of results for each processor supported by the Citrix Hypervisor host and for the control domain executing on the host
| Parameter | Description |
|---|---|
|
Test period |
How often should the test be executed. |
|
Host |
The host for which the test is to be configured. |
|
Xen User, Xen Password and Confirm Password |
To enable the eG agent to connect to the XenServer API for collecting statistics of interest, this test should login to the target hypervisor as a root user. Provide the name of the root user in the Xen User text box. Root user privileges are mandatory when monitoring a XenServer 5.5 (or below). However, if you are monitoring XenServer 5.6 (or above) and you prefer not to expose the credentials of the root user, then, you have the option of configuring a user with pool-admin privileges as the Xen User. If you do not want to expose the credentials of a root/pool-admin user, then you can configure the tests with the credentials of a Xen User with Read-only privileges to the XenServer. However, if this is done, then the Xen Uptime test will not run, and the Xen CPU and Xen Memory tests will not be able to report metrics for the control domain descriptor. To avoid such an outcome, do the following before attempting to configure the eG tests with a Xen User who has Read-only privileges to the Citrix Hypervisor:
Once this is done, you can configure the eG tests with the credentials of a Xen User with Read-only privileges. The password of the specified Xen User needs to be mentioned in the Xen Password text box. Then, confirm the Xen Password by retyping it in the Confirm Password text box. |
| SSL |
By default, the Citrix Hypervisor is not SSL-enabled. This indicates that by default, the eG agent communicates with the target hypervisor using HTTP. Accordingly, the SSL flag is set to No by default. If you configure the target hypervisor to use SSL, then make sure that the SSL flag is set to Yes, so that the eG agent communicates with the target hypervisor using HTTPS. Note that a default SSL certificate comes bundled with every Citrix Hypervisor installation. If you want the eG agent to use this default certificate for communicating with an SSL-enabled Citrix Hypervisor, then no additional configuration is required. However, if you do not want to use the default certificate, then you can generate a self-signed certificate for use by the target hypervisor. In such a case, you need to explicitly follow the broad steps given below to enable the eG agent to communicate with the target hypervisor via HTTPS:
For a detailed discussion on each of these steps, refer to the Troubleshooting section of this document. |
|
Webport |
By default, in most virtualized environments, the target hypervisor listens on port 80 (if not SSL-enabled) or on port 443 (if SSL-enabled). This implies that while monitoring an SSL-enabled Citrix hypervisor, the eG agent, by default, connects to port 443 of the server to pull out metrics, and while monitoring a non-SSL-enabled Citrix hypervisor, the eG agent connects to port 80. Accordingly, the webport parameter is set to 80 or 443 depending upon the status of the ssl flag. In some environments however, the default ports 80 or 443 might not apply. In such a case, against the webport parameter, you can specify the exact port at which the target hypervisor in your environment listens so that the eG agent communicates with that port. |
|
Detailed Diagnosis |
To make diagnosis more efficient and accurate, the eG suite embeds an optional detailed diagnostic capability. With this capability, the eG agents can be configured to run detailed, more elaborate tests as and when specific problems are detected. To enable the detailed diagnosis capability of this test for a particular server, choose the On option. To disable the capability, click on the Off option. The option to selectively enable/disable the detailed diagnosis capability will be available only if the following conditions are fulfilled:
|
Measurements made by the test
| Measurement | Description | Measurement Unit | Interpretation |
|---|---|---|---|
|
Physical CPU usage |
Indicates the percentage of physical CPU used by this processor or the control domain. |
Percent |
A very high value for this measure indicates excessive CPU utilization by that processor or control domain. The CPU utilization may be high because a few processes are consuming a lot of CPU, or because there are too many processes contending for a limited resource. If adequate CPU resources are not available to the host, then the guests too would experience a resource crunch; this in turn, could cause significant slowdowns in the execution of applications hosted by the guests. A high value for the control_domain descriptor indicates that one/more control domain processes are consuming CPU resources excessively. |
The detailed diagnosis capability that is available only for the control_domain descriptor, will list the CPU-intensive processes executing on the control domain. Resource intensive processes can be killed/stopped to avoid excessive CPU usage. Alternatively, administrators can allocate additional CPU resources to the host to ensure that processes have adequate memory for execution.
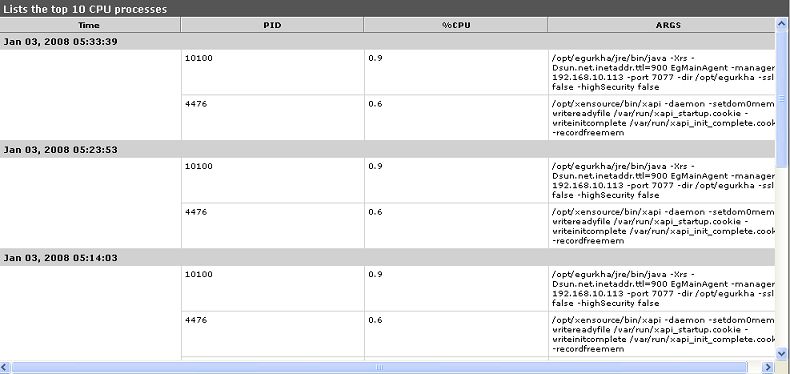
Figure 1 : The detailed diagnosis of the Physical CPU usage measure
Note:
In case of multi-processor systems, this test typically reports the CPU usage for every processor. The Summary descriptor reports the average CPU usage across processors.



