Wyse Terminals Test
Wyse thin clients are secure access devices that provide a simpler and easier way to deliver the productivity and application flexibility of a PC without the PC downside.
Users can connect to a Citrix server/server farm from a Wyse terminal to access critical applications. Whenever a user complaints of issues with his/her terminal, you can use this test to figure out which terminal the user is connecting from, whether that terminal is up and running, and if so, for how long.
This test is disabled by default. To enable the test, go to the enable / disable tests page using the menu sequence : Agents -> Tests -> Enable/Disable, pick the desired Component type, set Performance as the Test type, choose the test from the disabled tests list, and click on the < button to move the test to the ENABLED TESTS list. Finally, click the Update button.
Target of the test : A Citrix Virtual Apps server
Agent deploying the test : An internal agent
Outputs of the test : One set of outputs for every Wyse terminal user currently connected to the Citrix server
Configurable parameters for this test
- TEST PERIOD - How often should the test be executed
- Host - The host for which the test is to be configured.
- port - The port at which the host listens
- SNMPPort - The port number through which the Wyse terminal exposes its SNMP MIB. The default value is 161.
- SNMPVERSION – By default, the eG agent supports SNMP version 1. Accordingly, the default selection in the snmpversion list is v1. However, if a different SNMP framework is in use in your environment, say SNMP v2 or v3, then select the corresponding option from this list.
- SNMPCommunity – The SNMP community name that the test uses to communicate with the Cisco router. This parameter is specific to SNMP v1 and v2 only. Therefore, if the snmpversion chosen is v3, then this parameter will not appear.
- username – This parameter appears only when v3 is selected as the snmpversion. SNMP version 3 (SNMPv3) is an extensible SNMP Framework which supplements the SNMPv2 Framework, by additionally supporting message security, access control, and remote SNMP configuration capabilities. To extract performance statistics from the MIB using the highly secure SNMP v3 protocol, the eG agent has to be configured with the required access privileges – in other words, the eG agent should connect to the MIB using the credentials of a user with access permissions to be MIB. Therefore, specify the name of such a user against the username parameter.
- authpass – Specify the password that corresponds to the above-mentioned username. This parameter once again appears only if the snmpversion selected is v3.
- confirm password – Confirm the authpass by retyping it here.
-
authtype – This parameter too appears only if v3 is selected as the snmpversion. From the authtype list box, choose the authentication algorithm using which SNMP v3 converts the specified username and password into a 32-bit format to ensure security of SNMP transactions. You can choose between the following options:
- md5 – Message Digest Algorithm
- sha – Secure Hash Algorithm
- encryptflag – This flag appears only when v3 is selected as the snmpversion. By default, the eG agent does not encrypt SNMP requests. Accordingly, the encryptflag is set to no by default. To ensure that SNMP requests sent by the eG agent are encrypted, select the yes option.
-
encrypttype – If the encryptflag is set to yes, then you will have to mention the encryption type by selecting an option from the encrypttype list. SNMP v3 supports the following encryption types:
- des – Data Encryption Standard
- AES – Advanced Encryption Standard
- encryptpassword – Specify the encryption password here.
- confirm password – Confirm the encryption password by retyping it here.
- timeout - Specify the duration (in seconds) within which the SNMP query executed by this test should time out in the TIMEOUT text box. The default is 10 seconds.
- DATA OVER TCP – By default, in an IT environment, all data transmission occurs over UDP. Some environments however, may be specifically configured to offload a fraction of the data traffic – for instance, certain types of data traffic or traffic pertaining to specific components – to other protocols like TCP, so as to prevent UDP overloads. In such environments, you can instruct the eG agent to conduct the SNMP data traffic related to the equalizer over TCP (and not UDP). For this, set the data over tcp flag to Yes. By default, this flag is set to No.
-
detailed diagnosis - To make diagnosis more efficient and accurate, the eG Enterprise embeds an optional detailed diagnostic capability. With this capability, the eG agents can be configured to run detailed, more elaborate tests as and when specific problems are detected. To enable the detailed diagnosis capability of this test for a particular server, choose the On option. To disable the capability, click on the Off option.
The option to selectively enable/disable the detailed diagnosis capability will be available only if the following conditions are fulfilled:
- The eG manager license should allow the detailed diagnosis capability
- Both the normal and abnormal frequencies configured for the detailed diagnosis measures should not be 0.
|
Measurements made by the test
|
Uptime of Wyse terminal:
|
Indicates how long the Wyse terminal from which this user is connecting has been up and running.
|
Secs
|
A low reported by this measure could indicate that the Wyse terminal has rebooted recently.
|
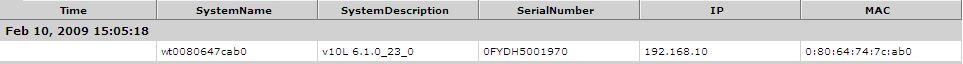
The detailed diagnosis of the Uptime of Wyse terminal measure reveals the name, serial number, IP address, and MAC address of the Wyse terminal from which the user is currently connecting to the Citrix server.
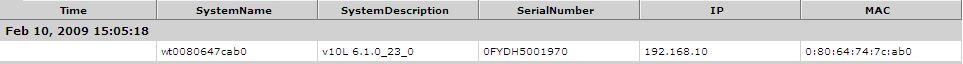
Figure 1 : The detailed diagnosis of the Uptime of Wyse terminal measure