Monitoring Microsoft Office 365
To monitor the managed Microsoft Office 365, login to the eG management console as a user with monitoring privileges.
Browse the Components At-A-Glance section of the Monitor Home page that appears, and locate the Microsoft Office 365 component type. Click on the bar that corresponds to this component type. This will lead you to the Layers tab page, where you can view the monitoring model for Microsoft Office 365 (see Figure 1).
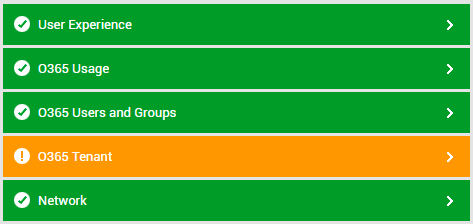
Figure 1 : Layer model for the Microsoft Office 365 component
Each layer of Figure 1 is mapped to tests that report on a wide variety of KPIs such as availability, service health, resource usage, and operational health of Office 365. Using these metrics, administrators can find quick and accurate answers to the following performance queries:
- Is HTTP/S connection to the Office 365 portal available? Was any latency noticed in the connection?
- Is network connection to Office 365 available? If so, how quickly is it responding to network requests?
- Were any groups modified recently? Were they distribution groups, dynamic distribution groups, Office 365 groups, or security groups?
- Are there any orphaned groups or empty groups? Which ones are they?
- Which is the default domain of the target Office 365 tenant? Is this domain verified? Which are the unverified domains in the monitored tenant?
- Has any Office 365 product run out of licenses or is about to? Is so, which one is it?
- Is any product's license nearing expiry?
- Which products are being used on a trial license?
- Was any announcement posted on the message center recently? If so, what is it?
- Are all Office 365 services functioning optimally? Is any service in a degraded state presently? If so, which one?
- Is any service experiencing a service incident? What type of an incident is it?
- Is any service under maintenance currently?
- Which service is pending provisioning?
- Which service has a high workload? What type of operations are imposing a heavy load on the service? Who is performing such operations?
- Are there any unlicensed users on Office 365? If so, who are they?
- Which users have been denied sign-in rights?
- Which users were deleted recently?
For more information on the Network layer, refer to the Monitoring Unix and Windows Servers document. This