Class Statistics Test
In order to analyze or control one type of traffic distinctly, PacketShaper must be able to differentiate it from other types of traffic. The traffic tree's traffic classes are PacketShaper's mechanism for identifying and organizing different types of traffic.
PacketShaper differentiates one application from another by evaluating characteristics in traffic flows and organizing them into classes. Each traffic class contains atleast one matching rule, a set of characteristics that identifies a specific traffic type.
Once a traffic class is created, it is a good practice to observe the traffic to and from each traffic class, so that you can check the effectiveness of the rules that you have set per traffic class. This is where the Class Statistics test helps. This test auto-discovers the traffic classes configured in the PacketShaper S-Series Load Balancer, monitors the volume of traffic sent and received by each traffic class, captures packet drops, hits to each class and the policy associated with the class, and enables administrators to determine the following:
- How well the load balancer accelerates/compresses traffic to/from traffic classes;
- Traffic classes for which matching rules may have to be fine-tuned
- Traffic classes on which maximum SYN attacks are blocked
Target of the test : PacketShaper Load Balancer S-Series
Agent deploying the test : An external agent
Outputs of the test : One set of the results for each traffic class configured on the target PacketShaper Load Balancer S-Series device that is being monitored
| Parameter | Description |
|---|---|
|
Test period |
How often should the test be executed |
|
Host |
The IP address of the host for which this test is to be configured. |
|
SNMPPort |
The port at which the monitored target exposes its SNMP MIB; the default is 161. |
|
SNMPVersion |
By default, the eG agent supports SNMP version 1. Accordingly, the default selection in the SNMPversion list is v1. However, if a different SNMP framework is in use in your environment, say SNMP v2 or v3, then select the corresponding option from this list. |
|
SNMPCommunity |
The SNMP community name that the test uses to communicate with the firewall. This parameter is specific to SNMP v1 and v2 only. Therefore, if the SNMPVersion chosen is v3, then this parameter will not appear. |
|
Username |
This parameter appears only when v3 is selected as the SNMPversion. SNMP version 3 (SNMPv3) is an extensible SNMP Framework which supplements the SNMPv2 Framework, by additionally supporting message security, access control, and remote SNMP configuration capabilities. To extract performance statistics from the MIB using the highly secure SNMP v3 protocol, the eG agent has to be configured with the required access privileges – in other words, the eG agent should connect to the MIB using the credentials of a user with access permissions to be MIB. Therefore, specify the name of such a user against this parameter. |
|
Context |
This parameter appears only when v3 is selected as the SNMPVERSION. An SNMP context is a collection of management information accessible by an SNMP entity. An item of management information may exist in more than one context and an SNMP entity potentially has access to many contexts. A context is identified by the SNMPEngineID value of the entity hosting the management information (also called a contextEngineID) and a context name that identifies the specific context (also called a contextName). If the Username provided is associated with a context name, then the eG agent will be able to poll the MIB and collect metrics only if it is configured with the context name as well. In such cases therefore, specify the context name of the Username in the Context text box. By default, this parameter is set to none. |
|
AuthPass |
Specify the password that corresponds to the above-mentioned Username. This parameter once again appears only if the SNMPversion selected is v3. |
|
Confirm Password |
Confirm the AuthPass by retyping it here. |
|
AuthType |
This parameter too appears only if v3 is selected as the SNMPversion. From the AuthType list box, choose the authentication algorithm using which SNMP v3 converts the specified username and password into a 32-bit format to ensure security of SNMP transactions. You can choose between the following options:
|
|
EncryptFlag |
This flag appears only when v3 is selected as the SNMPversion. By default, the eG agent does not encrypt SNMP requests. Accordingly, the this flag is set to No by default. To ensure that SNMP requests sent by the eG agent are encrypted, select the Yes option. |
|
EncryptType |
If the EncryptFlag is set to Yes, then you will have to mention the encryption type by selecting an option from the EncryptType list. SNMP v3 supports the following encryption types:
|
|
EncryptPassword |
Specify the encryption password here. |
|
Confirm Password |
Confirm the encryption password by retyping it here. |
|
Timeout |
Specify the duration (in seconds) within which the SNMP query executed by this test should time out in this text box. The default is 10 seconds. |
|
EngineID |
This parameter appears only when v3 is selected as the SNMPVersion. Sometimes, the test may not report metrics when AES192 or AES256 is chosen as the Encryption type. To ensure that the test report metrics consistently, administrators need to set this flag to Yes. By default, this parameter is set to No. |
|
Data Over TCP |
By default, in an IT environment, all data transmission occurs over UDP. Some environments however, may be specifically configured to offload a fraction of the data traffic – for instance, certain types of data traffic or traffic pertaining to specific components – to other protocols like TCP, so as to prevent UDP overloads. In such environments, you can instruct the eG agent to conduct the SNMP data traffic related to the monitored target over TCP (and not UDP). For this, set this flag to Yes. By default, this flag is set to No. |
|
Detailed Diagnosis |
To make diagnosis more efficient and accurate, the eG Enterprise embeds an optional detailed diagnostic capability. With this capability, the eG agents can be configured to run detailed, more elaborate tests as and when specific problems are detected. To enable the detailed diagnosis capability of this test for a particular server, choose the On option. To disable the capability, click on the Off option. The option to selectively enable/disable the detailed diagnosis capability will be available only if the following conditions are fulfilled:
|
| Measurement | Description | Measurement Unit | Interpretation |
|---|---|---|---|
|
Class hits |
Indicates the number of times traffic flows matched this traffic class. |
Number |
Class hits occur only at the beginning of a traffic flow or session. The detailed diagnosis of this measure lists the name of the partition, link direction, class rate and current class rate. |
|
Policy hits |
Indicates the number of times policy applied to this traffic class was hit. |
Number |
A policy determines how an application's individual flows are treated in the context of competing applications, and allows you to manage bandwidth management on a flow-by-flow basis.With policies, you can give each flow of mission-critical traffic the bandwidth it needs for optimum performance, as well as protect it from greedy, less important traffic. In addition, policies can keep non-urgent traffic flows (such as FTP) from consuming more than an appropriate share of bandwidth. |
|
Data transmission |
Indicates the amount of data transmitted using this traffic class during the last measurement period. |
MB |
|
|
Data retransmission |
Indicates the amount of data was retransmitted using this traffic class during the last measurement period. |
MB |
If large amount of data takes too long to be successfully retransmitted, you may have to figure out what is causing repeated retransmission failures and fix it before packet loss occurs. |
|
Packets transmission |
Indicates the number of packets that were transmitted using this traffic class during the last measurement period. |
Number |
|
|
TCP data packets transmission |
Indicates the number of TCP data packets that were transmitted using this traffic class during the last measurement period. |
Number |
|
|
TCP data packets retransmission |
Indicates the number of TCP data packets that were retransmitted using this traffic class during the last measurement period. |
Number |
If TCP packets take too long to be successfully retransmitted, you may have to figure out the real reason behind repeated retransmission failures and fix it before packet loss occurs. |
|
Client side blocked SYN attack |
Indicates the number of SYN flood attacks blocked on a client for this traffic class during the last measurement period. |
Number |
A SYN attack involves a system sending hundreds of requests to a server over the Internet. Ideally, the value of this measure should be zero. |
|
Server side blocked SYN attack |
Indicates the number of SYN flood attacks blocked on a server for this traffic class during the last measurement period. |
Number |
Ideally, the value of this measure should be zero. |
The detailed diagnosis of the Class hits measure lists the name of the partition, link direction, class rate and current class rate.
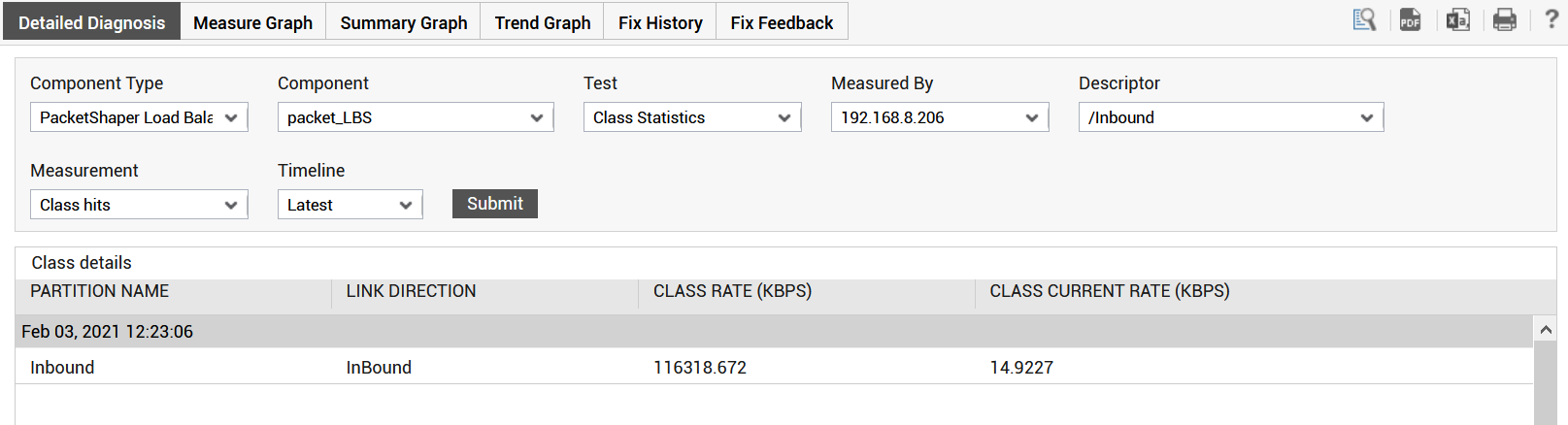
Figure 1 : The detailed diagnosis of the Class hits measure
