How to Manage Components in an Agentless Manner?
While adding a new component using the eG administrative interface, the eG Enterprise system requests the administrator to indicate whether the component being added supports agentless monitoring or not (see Figure 2). This option appears only if at least one remote agent has been configured for the target environment. Otherwise, agent-based monitoring is used by default.
To manage a new component in an agentless manner, do the following:
-
Click the Agentless check box in Figure 1.
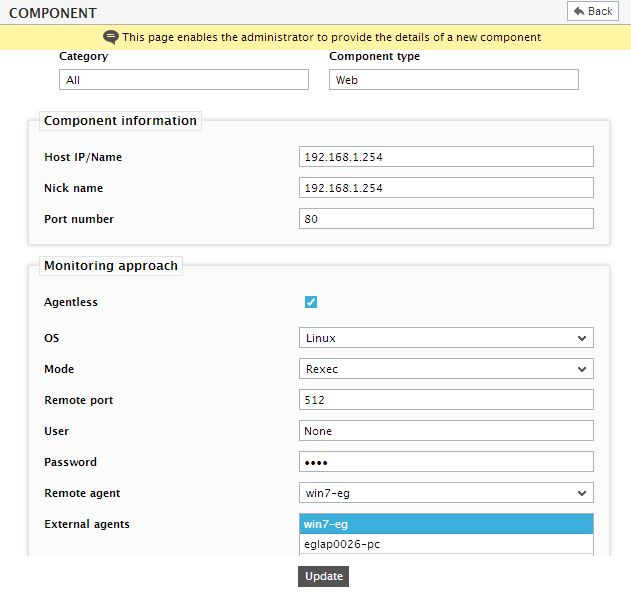
Figure 1 : Enabling agentless monitoring for a Linux component with Rexec as the Mode
-
Next, select the operating system of the component to be monitored from the os list box (see Figure 1). Remote agents can extract measures from all the eG-supported platforms (Windows 8/2012, Linux, Solaris, HPUX, AIX, Tru64). If a Unix operating system is selected (i.e. Linux/Solaris/HPUX/AIX/Tru64) as the os, then the following sequence of steps will apply:
- As soon as any of the Unix platforms is selected from the os list box, Rexecis displayed against Mode. Rexec executes commands remotely on a Unix host. Before proceeding with Rexec, make sure that the Rexec-related pre-requisites detailed in Pre-requisites for Monitoring a Unix System/Application in an Agentless Manner are fulfilled.
- The default port number of the Rexec command is 512, which will be displayed against the Remote port field.
-
The rexec command requires a valid user name and password at the remote host to connect to it. Therefore, provide the necessary login credentials against the User and Password text boxes.
Note:
While connecting to a remote host, Rexec sends passwords in clear text, and hence can be used only in secure environments. ssh is a more secure alternative
-
Alternatively, you can choose ssh as the Mode (see Figure 2). Before proceeding with the ssh mode, make sure that the SSH-related pre-requisites detailed in Pre-requisites for Monitoring a Unix System/Application in an Agentless Manner are fulfilled.
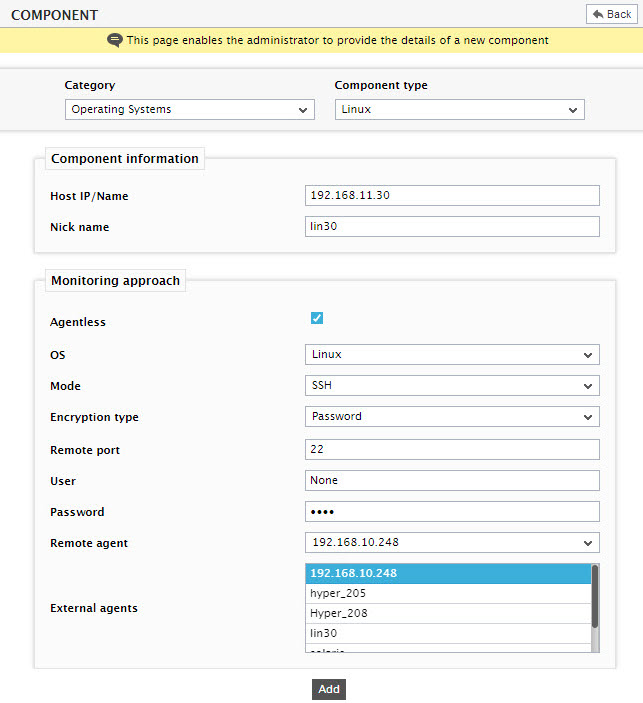
Figure 2 : Enabling agentless monitoring of a Linux component with SSH as the Mode
- As stated in the Pre-requisites section ( Pre-requisites for Monitoring a Unix System/Application in an Agentless Manner), if ssh is chosen as the Mode, then you will also have to indicate the Encryption type for your SSH connection. By default, Password is set as the encryption type. If need be, you can select Keybased as the Encryption type.
- If Encryption type is set to Keybased, you will have to specify a Key file name. Here, specify the full path to the private key file id_rsa, which will be available in the location, <EG_AGENT_INSTALL_DIR>\agent\sshkeys. For instance, if the eG agent has been installed in the D:\eGurkha folder, your Key file name will be: D:\eGurkha\agent\sshkeys\id_rsa
- The port number for secure shell access has to be specified against Remote port field. By default, 22 is the port at which the SSH server listens.
- Regardless of the Encryption type chosen, provide the valid User name and Password using which the SSH connection to the host is to be established. Against User, provide the name of the user as who you logged into the target Unix host for copying the authorization_keys file (see point 2 of Pre-requisites for Monitoring a Unix System/Application in an Agentless Manner). Against Password, specify the pass phrase that is associated with the private key file, id_rsa. If you are using the default public/private keys bundled with the eG agent, eginnovations will be the pass phrase.
-
On the other hand, if a Windows operating system (Windows 8/2012) is selected from the os list box, then the Mode will change to Perfmon. Before selecting Perfmon as the Mode, make sure that the pre-requisites detailed in Pre-requisites for Monitoring a Windows System/Application in an Agentless Manner
Note:
Besides ssh and remote Perfmon, agentless monitoring can be done using SNMP and externally accessible APIs/protocols (e.g., SQL for Oracle, MQ API for IBM MQ, HTTP for WebLogic, Web Service, CLI for storage devices etc.).
-
From the list of remote agents configured in the, select the remote agent that will monitor the component being added (see Figure 3).
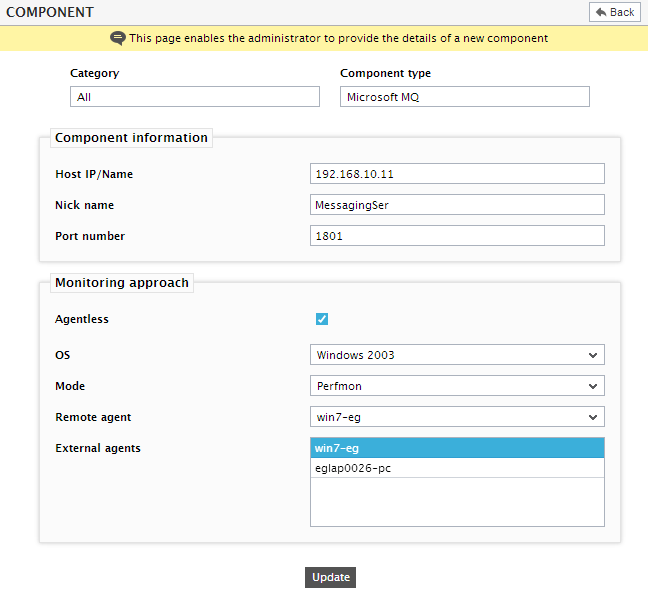
Figure 3 : Enabling Agentless support for a Windows component
-
Finally, associate one or more External agents with the component, and click the Update button to complete the configuration.
Note:
- Like other agent types, remote agents too communicate with the eG manager through HTTP/HTTPS.
- A single agent can function as a remote agent as well as an external agent. However, an external agent for which client emulation has been enabled cannot function as a remote agent.
Note:
It is recommended that a remote agent be used to support up to 10 targets.