Top Sources By Interfaces Test
If the Network Interfaces test reveals that a specific interface is handling an abnormally high volume of traffic or is consuming bandwidth resources excessively, you may want to know where this traffic is originating from. This is where the Top Sources test helps!
The Top Sources test reveals those hosts whose interactions with other hosts in the environment are resulting in large volumes of data being transmitted over a network interface. In the event of a network slowdown, you can use this test to accurately identify hosts whose current network activities are 'suspect' - i.e., you can isolate those hosts that may be engaged in bandwidth-intensive transactions with other hosts, and could hence be contributing to the slowdown.
Target of the test : A Netflow Device
Agent deploying the test : An external agent
Outputs of the test : One set of results for each of the top-n sources (in terms of traffic volume) communicating through each interface of the target network device.
First level descriptor: Interface
Second level descriptor: Source host's IP address
Metrics are also reported for an Others descriptor. Netflow statistics pertaining to all sources that are not the top-n sources are aggregated and presented against the Others descriptor for each interface.
| Parameter | Description |
|
Test period |
How often should the test be executed |
|
Host |
The host for which the test is to be configured. |
|
Filter By, Minimum Flow Percent, Report Top N Flows, Show DD for Top N Flows |
By default, for each interface that the target Netflow device supports, this test reports metrics for only the top-10 sources that handle over 3% of the total traffic on that interface. Also, by default, the test will report detailed diagnostics for only the top-5 sources that handle over 3% of the total traffic on that interface. This default setting enables network administrators to focus on the abnormal flows alone. This behavior is governed by the default setting of the Filter By, Minimum Flow Percent, Report Top N Flows, and Show DD for Top N Flows parameters. By default, the Filter By option is set to %Traffic and the Minimum Flow Percent is set to 3 (%). You can increase or decrease the Minimum Flow Percent depending upon the level of traffic that you deem as abnormal. Also, by default, the Report Top N Flows is set to 10 and Show DD for Top N Flows is set to 5. You can increase or decrease the value of these two parameters depending upon the level of visibility you require. You can also override the Filter By default setting and have this test report real-time metrics and detailed diagnostics for only those sources (per interface) that use over a configured percentage of bandwith resources when transmitting data. For this, set Filter By to Bandwidth Used and configure a bandwidth usage limit (in %) against Minimum Flow Percent. This way, administrators can focus on only those sources that generate bandwidth-intensive traffic. |
|
Exclude Sources |
Provide a comma-separated list of sources that you want excluded from monitoring. For example, your specification can be, 192.168.10.45, 192.168.10.71,192.168.10.220. You can even provide patterns of source IP addresses as a comma-separated list - for instance, 192.168.10.*,192.168.8.1*1, *.168.9.45. Alternatively, you can provide a range of source IP addresses. For example, 192.168.10.32-192.168.10.45. Note: Sources can be represented using IP addresses only and not host names. |
|
Exclude Destinations |
Provide a comma-separated list of destinations that you want excluded from monitoring. For example, your specification can be, 192.168.10.45, 192.168.10.71,192.168.10.220. You can even provide patterns of destination IP addresses as a comma-separated list - for instance, 192.168.10.*,192.168.8.1*1, *.168.9.45. Alternatively, you can provide a range of source IP addresses. For example, 192.168.10.32-192.168.10.45. Note: Destinations can be represented using IP addresses only and not host names. |
|
Exclude Interfaces |
Provide a comma-separated list of interfaces that you want excluded from monitoring. For example, your specification can be, FastEtherNet0/0, FastEthernet0/1,FastEtherNet0/2. You can even provide patterns of interfaces as a comma-separated list - for instance, *ethernet*,Fast*. |
|
Show Host Names |
This test captures statistics on traffic that originates from source hosts, where each host is by default represented by its IP address in the eG monitoring console. Accordingly, this flag is set to No by default. You can set this flag to Yes so that the names of the individual hosts are displayed in the eG monitoring console instead of their IP addresses. |
|
Show Traffic |
By default, the Both Traffic option is chosen from the Show Traffic drop-down list. This implies that by default, this test will report metrics on both input and output traffic for every interface. In some environments, the traffic flowing out of one interface (i.e., output traffic) can subsequently flow into another interface (i.e., input traffic). In such environments, if the eG agent is configured to report on both input and output traffic, duplication of metrics may become inevitable. As a result, administrators may not be able to assess the real data load on any interface. To avoid this, you can override the default setting of the Show Traffic parameter by choosing one of the following options:
|
|
Report By Interface Type |
By default, this flag is set to No. This means that by default, this test will report metrics for every interface that the target NetFlow device supports. If you want, you can configure this test to report metrics for every Interface_Type:Interface_Name pair. For this, set this flag to Yes. Doing so will help you quickly determine what is the type of every interface, and whether the interface type influences traffic flow and bandwidth consumption in any way. |
|
Ignore Local Traffic |
By default, this flag is set to Yes, indicating that the test will ignore the sources of all the intranet traffic on the router. If you want the test to report metrics pertaining to the sources of local traffic as well, set this flag to No. |
|
Process Tainted Packets |
Network latencies and processing bottlenecks can sometimes cause netflow records to be transmitted slowly to the NetFlow collector. In such a situation, you can instruct the collector to either process or ignore the delayed NetFlow records. If you want the metrics reported to pertain to current NetFlow records only, then you may choose to ignore the delayed records. In this case, set this flag to No. If you want old NetFlow records to also be considered when identifying top sources and reporting their traffic statistics, then set this flag to Yes. Typically, any NetFlow record that takes 10 minutes or over to reach the NetFlow collector is deemed a tainted/delayed record. |
|
Sampling, Sampling Rate |
By default, NetFlow is designed to process all IP packets on an interface. This is why, the Sampling flag is set to No by default. In some environments however, e.g. on Internet backbones, processing all IP packets can be too costly, due to the extra processing required for each packet and large number of simultaneous flows. This is where sampling is useful. In such environments, set the Sampling flag to Yes. Once this is done, then each interface will process only 1 packet out of a configured number of packets. Specify the number of packets from which this 1 packet should be picked in the Sampling Rate text box. For instance, to pick 1 out of 1000 packets for sampling, set the Sampling Rate to 1000. Where Sampling is enabled, all NetFlow metrics - particularly, metrics on traffic volume - will be adjusted based on the Sampling Rate you specify. |
|
SNMPPort |
The port at which the monitored target exposes its SNMP MIB; the default is 161. |
|
SNMPversion |
By default, the eG agent supports SNMP version 1. Accordingly, the default selection in the snmpversion list is v1. However, if a different SNMP framework is in use in your environment, say SNMP v2 or v3, then select the corresponding option from this list. |
|
SNMPCommunity |
The SNMP community name that the test uses to communicate with the firewall. This parameter is specific to SNMP v1 and v2 only. Therefore, if the SNMPVersion chosen is v3, then this parameter will not appear. |
|
Username |
This parameter appears only when v3 is selected as the SNMP. SNMP version 3 (SNMPv3) is an extensible SNMP Framework which supplements the SNMPv2 Framework, by additionally supporting message security, access control, and remote SNMP configuration capabilities. To extract performance statistics from the MIB using the highly secure SNMP v3 protocol, the eG agent has to be configured with the required access privileges – in other words, the eG agent should connect to the MIB using the credentials of a user with access permissions to be MIB. Therefore, specify the name of such a user against the Username parameter. |
|
Context |
This parameter appears only when v3 is selected as the SNMPversion. An SNMP context is a collection of management information accessible by an SNMP entity. An item of management information may exist in more than one context and an SNMP entity potentially has access to many contexts. A context is identified by the SNMPEngineID value of the entity hosting the management information (also called a contextEngineID) and a context name that identifies the specific context (also called a contextName). If the username provided is associated with a context name, then the eG agent will be able to poll the MIB and collect metrics only if it is configured with the context name as well. In such cases therefore, specify the context name of the Username in the context text box. By default, this parameter is set to none. |
|
Authpass |
Specify the password that corresponds to the above-mentioned Username. This parameter once again appears only if the SNMPversion selected is v3. |
|
Confirm password |
Confirm the Authpass by retyping it here. |
|
Authtype |
This parameter too appears only if v3 is selected as the SNMPversion. From the AuthType list box, choose the authentication algorithm using which SNMP v3 converts the specified username and password into a 32-bit format to ensure security of SNMP transactions. You can choose between the following options:
|
|
Encryptflag |
This flag appears only when v3 is selected as the SNMPversion. By default, the eG agent does not encrypt SNMP requests. Accordingly, this flag is set to No by default. To ensure that SNMP requests sent by the eG agent are encrypted, select the Yes option. |
|
Encrypttype |
If the EncryptFlag is set to Yes, then you will have to mention the encryption type by selecting an option from the EncryptType list. SNMP v3 supports the following encryption types:
|
|
Encryptpassword |
Specify the encryption password here. |
|
Confirm Password |
Confirm the encryption password by retyping it here. |
|
Timeout |
Specify the duration (in seconds) within which the SNMP query executed by this test should time out in this text box. The default is 10 seconds. |
|
Data Over TCP |
By default, in an IT environment, all data transmission occurs over UDP. Some environments however, may be specifically configured to offload a fraction of the data traffic – for instance, certain types of data traffic or traffic pertaining to specific components – to other protocols like TCP, so as to prevent UDP overloads. In such environments, you can instruct the eG agent to conduct the SNMP data traffic related to the monitored target over TCP (and not UDP). For this, set this flag to Yes. By default, this flag is set to No. |
|
Engine ID |
This parameter appears only when v3 is selected as the SNMPVersion. Sometimes, the test may not report metrics when AES192 or AES256 is chosen as the Encryption type. To ensure that the test report metrics consistently, administrators need to set this flag to Yes. By default, this parameter is set to No. |
|
DD Frequency |
Refers to the frequency with which detailed diagnosis measures are to be generated for this test. The default is 1:1. This indicates that, by default, detailed measures will be generated every time this test runs, and also every time the test detects a problem. You can modify this frequency, if you so desire. Also, if you intend to disable the detailed diagnosis capability for this test, you can do so by specifying none against DD frequency. |
|
Detailed Diagnosis |
To make diagnosis more efficient and accurate, the eG Enterprise embeds an optional detailed diagnostic capability. With this capability, the eG agents can be configured to run detailed, more elaborate tests as and when specific problems are detected. To enable the detailed diagnosis capability of this test for a particular server, choose the On option. To disable the capability, click on the Off option. The option to selectively enable/disable the detailed diagnosis capability will be available only if the following conditions are fulfilled:
|
| Measurement | Description | Measurement Unit | Interpretation |
|---|---|---|---|
|
Total data exchange |
Indicates the total amount of data transmitted and received by this source during the last measurement period. |
KB |
Compare the value of this measure across sources to identify which source host is contributing to the high level of network traffic. Use the detailed diagnosis of this measure to determine the top netflows (in terms of the volume of data transacted) that originated from this source, and the amount of data transacted in bytes and packets in every flow. Note: By default, for any interface, the value of this measure will include both incoming and outgoing traffic. However, if the Show Traffic flag is set to IN Traffic Only, then the value of this measure will not include output traffic; instead, only the input traffic flowing into an interface will be considered when reporting this measure. Similarly, if the Show Traffic flag is set to OUT Traffic Only, then the output traffic of an interface will alone be considered when computing the value of this measure. The input traffic will be disregarded in this case. |
|
Total packets exchange |
Indicates the total number of packets transmitted and received by this source during the last measurement period. |
Packets |
Compare the value of this measure across sources to identify which source host is contributing to the high level of network traffic. Note: By default, for any interface, the value of this measure will include both incoming and outgoing traffic. However, if the Show Traffic flag is set to IN Traffic Only, then the value of this measure will not include output traffic; instead, only the input traffic flowing into an interface will be considered when reporting this measure. Similarly, if the Show Traffic flag is set to OUT Traffic Only, then the output traffic of an interface will alone be considered when computing the value of this measure. The input traffic will be disregarded in this case. |
|
Data exchange rate |
Indicates the rate at which this source transmitted/received data. |
Kbps |
By default, for any interface, the value of this measure will include both incoming and outgoing traffic. However, if the Show Traffic flag is set to IN Traffic Only, then the value of this measure will not include output traffic; instead, only the input traffic flowing into an interface will be considered when reporting this measure. Similarly, if the Show Traffic flag is set to OUT Traffic Only, then the output traffic of an interface will alone be considered when computing the value of this measure. The input traffic will be disregarded in this case. |
|
Packets exchange rate |
Indicates the rate at which this source transmitted/received packets. |
Kbps |
By default, for any interface, the value of this measure will include both incoming and outgoing traffic. However, if the Show Traffic flag is set to IN Traffic Only, then the value of this measure will not include output traffic; instead, only the input traffic flowing into an interface will be considered when reporting this measure. Similarly, if the Show Traffic flag is set to OUT Traffic Only, then the output traffic of an interface will alone be considered when computing the value of this measure. The input traffic will be disregarded in this case. |
|
Total traffic from this source |
Indicates what percentage of the total traffic on this interface was from this source. |
Percent |
A value close to 100% for this measure indicates that traffic from this source is imposing the maximum load on the network. If users complain of a latent network, you can compare the value of this measure across sources to accurately identify the source that is responsible for any congestion on the network. Note: By default, for any interface, the value of this measure will include both incoming and outgoing traffic. However, if the Show Traffic flag is set to IN Traffic Only, then the value of this measure will not include output traffic; instead, only the input traffic flowing into an interface will be considered when reporting this measure. Similarly, if the Show Traffic flag is set to OUT Traffic Only, then the output traffic of an interface will alone be considered when computing the value of this measure. The input traffic will be disregarded in this case. |
|
Total bandwidth utilization |
Indicates the bandwidth utilized by this source. |
Percent |
A value close to 100% indicates that this source is indicative of excessive bandwidth utilization by this source when transmitting data. If users complain of a latent network, you can compare the value of this measure across sources to accurately identify the source that is responsible for any congestion on the network. |
|
In traffic |
Indicates what percentage of total incoming traffic on this interface pertains to this source. |
Percent |
If the Show Traffic flag is set to OUT Traffic Only, then this measure will ot report any values for any interface. |
|
Out traffic |
Indicates what percentage of total outgoing traffic on this interface pertains to this source. |
Percent |
If the Show Traffic flag is set to IN Traffic Only, then this measure will ot report any values for any interface. |
|
Ingress bandwidth utilization |
Indicates the percentage of bandwidth utilized by traffic coming into this interface when receiving data from this source and receiving data for this source from destinations. |
Percent |
A value close to 100% is a cause for concern as it implies a potential congestion in incoming traffic on this interface. Note: This measure will be reported for an interface only if the Show Traffic parameter is set to IN Traffic Only or Both Traffic. |
|
Egress bandwidth utilization |
Indicates the percentage of bandwidth utilized by traffic going out of this interface when transmitting data to this source and when transmitting data for this source to destinations. |
Percent |
A value close to 100% is a cause for concern as it implies a potential congestion in outgoing traffic on this interface. Note: This measure will be reported for an interface only if the Show Traffic parameter is set toOUT Traffic Only or Both Traffic. |
|
Data received |
Indicates the amount of data received by this source. |
KB |
Compare the value of this measure across sources to know which source is receiving maximum data over this interface. Note: This measure will be reported for an interface only if the Show Traffic parameter is set to IN Traffic Only or Both Traffic. |
|
Data sent |
Indicates the amount of data sent by this source. |
KB |
Compare the value of this measure across sources to know which source is transmitting maximum data over this interface. Note: This measure will be reported for an interface only if the Show Traffic parameter is set to OUT Traffic Only or Both Traffic. |
|
Packets received |
Indicates the number of packets sent by this source. |
Number |
This measure will be reported for an interface only if the Show Traffic parameter is set to IN Traffic Only or Both Traffic. |
|
Packets sent |
Indicates the number of packets received by this source. |
Number |
This measure will be reported for an interface only if the Show Traffic parameter is set to OUT Traffic Only or Both Traffic. |
|
Data received rate |
Indicates the rate at which data is received by this source. |
Kbps |
If the value of this measure consistently drops for this source, it could indicate an incoming traffic congestion. Note: This measure will be reported for an interface only if the Show Traffic parameter is set to IN Traffic Only or Both Traffic. |
|
Data transmitted rate |
Indicates the rate at which data is sent by this source. |
Kbps |
If the value of this measure consistently drops for this source, it could indicate an outgoing traffic congestion. Note: This measure will be reported for an interface only if the Show Traffic parameter is set to OUT Traffic Only or Both Traffic |
|
Packets received rate |
Indicates the rate at which packets are received by this source. |
Packets/Sec |
If the value of this measure consistently drops for this source, it could indicate an incoming traffic congestion. Note: This measure will be reported for an interface only if the Show Traffic parameter is set to IN Traffic Only or Both Traffic. |
|
Packets transmitted rate |
Indicates the rate at which packets are transmitted by this source. |
Packets/Sec |
If the value of this measure consistently drops for this source, it could indicate an outgoing traffic congestion. Note: This measure will be reported for an interface only if the Show Traffic parameter is set to OUT Traffic Only or Both Traffic. |
Use the detailed diagnosis of the Total data exchange measure to determine the top netflows (in terms of the volume of data transacted) that originated from a particular source, and the amount of data and packets received. With the help of this detailed diagnosis, you can quickly compare the top netflows, know which netflow generated the maximum traffic, and figure out which destination that traffic was headed to. Once the problem destination is isolated, you can then investigate why traffic to that destination was high - is it because of the type of application executing on that destination? (eg., an online game or a movie that would typically consume a lot of bandwidth), or is it because of a poor network line connecting the source and the destination?
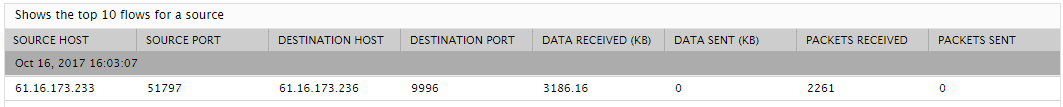
Figure 1 : The detailed diagnosis of the Total data exchange measure