Sharing and Access Request Activities Report
In SharePoint Online environments, administrators need to maintain the security and integrity of the data stored in the sites regardless of how the contents of the site are accessed (whether it is by requesting access, or via sharing invitations, or via sharing links). A security lapse may expose the contents of the site to malicious attacks. To ensure that sensitive activities are performed by authorized individuals alone, administrators need to periodically audit these sensitive activities. For this purpose, eG Enterprise offers a Sharing and Access Request Activities report. By generating this report, administrators can historically analyze the access requests, sharing invitations and sharing links, and closely scrutinize them to understand who initiated the operation frequently, on which site, and from where.
To generate the report, do the following:
- Follow the menu sequence: REPORTS BY FUNCTION -> Domain-specific Reports -> Microsoft SharePoint -> Sharing and Access Request Activities.
-
Figure 1 then appears. In Figure 1, select a criteria for analysis from the Analyze By list box.
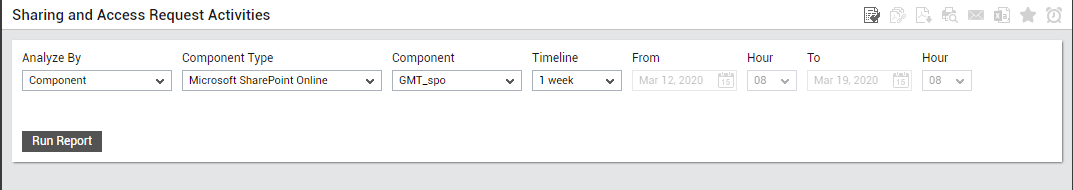
Figure 1 : Specifying the criteria for generating the Sharing and Access Request Activities report
-
Using this report, you can analyze the sharing-related operations performed by the users on one/more managed components, or those that are part of a zone, service or segment. The options provided by the Analyze By list box are discussed hereunder:
- Component: Select this option to choose the component(s) from across all the managed components in the environment.
- Zone: To generate a report for one/more components that are included in a zone, pick the Zone option. A Zone drop-down list will then appear, from which you would have to select the zone to which the components of interest to you belong. A Sub zone flag also appears. Indicate whether the components present within the sub-zones of the chosen zone are also to be to be considered for report generation, by setting the Sub zone flag to Yes.
- Segment: If you want to generate a report for one/more chosen components that belong to a segment, select the Segment option from Analyze By list box, and then pick the Segment from the drop-down list that appears.
- Service: If you want to generate a report for one/more components involved in the delivery of a service, select the Service option from Analyze By, and then pick the required Service from the drop-down list that appears.
- Choose a Component Type for which the report is to be generated.
- The Components list will now be populated with all the components that are managed in your environment for the chosen component type. If the Components list consists of too many components, then viewing all the components and selecting the ones you need for report generation could require endless scrolling. To avoid this, you can click the
 button next to the Components list. A Components pop up window will then appear using which you can view almost all the components in a single interface and Select the ones to be included in this report.
button next to the Components list. A Components pop up window will then appear using which you can view almost all the components in a single interface and Select the ones to be included in this report. -
Then, specify the Timeline for generating this report. You can either provide a fixed time line such as 1 hour, 2 days, etc., or select the Any option from the list to provide a From and To date/time for report generation.
Note:
For every user registered with the eG Enterprise system, the administrator can indicate the maximum timeline for which that user can generate a report. Once the maximum timeline is set for a user, then, whenever that user logs into eG Reporter and attempts to generate a report, the Timeline list box in the report page will display options according to the maximum timeline setting of that user. For instance, if a user can generate a report for a maximum period of 3 days only, then 3 days will be the highest option displayed in the Timeline list - i.e., 3 days will be the last option in the fixed Timeline list. Similarly, if the user chooses the Any option from the Timeline list and proceeds to provide a start date and end date for report generation using the From and To specifications, eG Enterprise will first check if the user's Timeline specification conforms to his/her maximum timeline setting. If not, report generation will fail. For instance, for a user who is allowed to generate reports spanning over a maximum period of 3 days only, the difference between the From and To dates should never be over 3 days. If it is, then, upon clicking the Run Report button a message box will appear, prompting the user to change the From and To specification.
-
In addition to the settings discussed above, this report comes with a set of default specifications. These settings are hidden by default. If you do not want to disturb these default settings, then you can proceed to generate the report by clicking the Run Report button soon after you pick one/more components for report generation. However, if you want to view and then alter these settings (if required), click on the
 icon. The default settings will then appear in the MORE OPTIONS drop down window (See Figure 2). The steps below discuss each of these settings and how they can be customized.
icon. The default settings will then appear in the MORE OPTIONS drop down window (See Figure 2). The steps below discuss each of these settings and how they can be customized.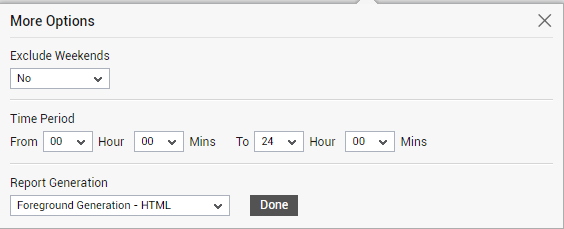
-
If the timeline specified for the report needs to exclude the data collected during the Weekends, then set Exclude weekends to Yes. If not, select No.
Note:
By default, the weekend constitutes Saturday and Sunday. To override this default setting, do the following:
- Edit the eg_report.ini file in the <EG_INSTALL_DIR>\manager\config directory.
- In the [EXCLUDE_WEEKEND] section of the file, the Days parameter is set to Saturday,Sunday by default. You can modify this by setting the Days parameter to a comma-separated list of other days of the week - say Friday,Saturday.
- Save the file after making the required changes.
-
Next, indicate the report Time period.
Note:
By default, the Time period is set to 24 hours. Accordingly, the From and To parameters in the [timeframe] section of the eg_report.ini file (in the <eg_install_dir>\manager\config directory) are set to 00:00 and 24:00 respectively. If need be, you can override this default setting by configuring a different timeframe against the From and/or To parameters.
-
In large environments, reports generated using months of data can take a long time to complete. Administrators now have the option of generating reports on-line or in the background. When a report is scheduled for background generation, administrators can proceed with their other monitoring, diagnosis, and reporting tasks, while the eG manager is processing the report. This saves the administrator valuable time. To schedule background processing of a report, you can either select the Background Save - PDF option from the Report Generation list. To process reports in the foreground, select the Foreground Generation - HTML option from this list.
Note:
- The Report Generation list will appear only if the EnableBackgroundReport flag in the [BACKGROUND_PROCESS] section of the eg_report.ini file (in the <EG_INSTALL_DIR>\manager\config directory) is set to Yes.
- The default selection in the Report Generation list will change according to the Timeline specified for the report. If the Timeline set is greater than or equal to the number of days specified against the MinDurationForReport parameter in the [BACKGROUND_PROCESS] section of the eg_report.ini file, then the default selection in the Report Generation list will be Background Save - PDF. On the other hand, if the Timeline set for the report is lesser than the value of the MinDurationForReport parameter, then the default selection in the Report Generation list will be Foreground. This is because, the MinDurationForReport setting governs when reports are to be processed in the background. By default, this parameter is set to 2 weeks - this indicates that by default, reports with a timeline of 2 weeks and above will be processed in the background.
- Click the Done button if any changes were made to the More Options drop down window.
- Finally, click the Run Report button to generate the report.
-
If the Report type is Foreground Generation - HTML, then Figure 3 will appear as soon as you click the Run Report button.
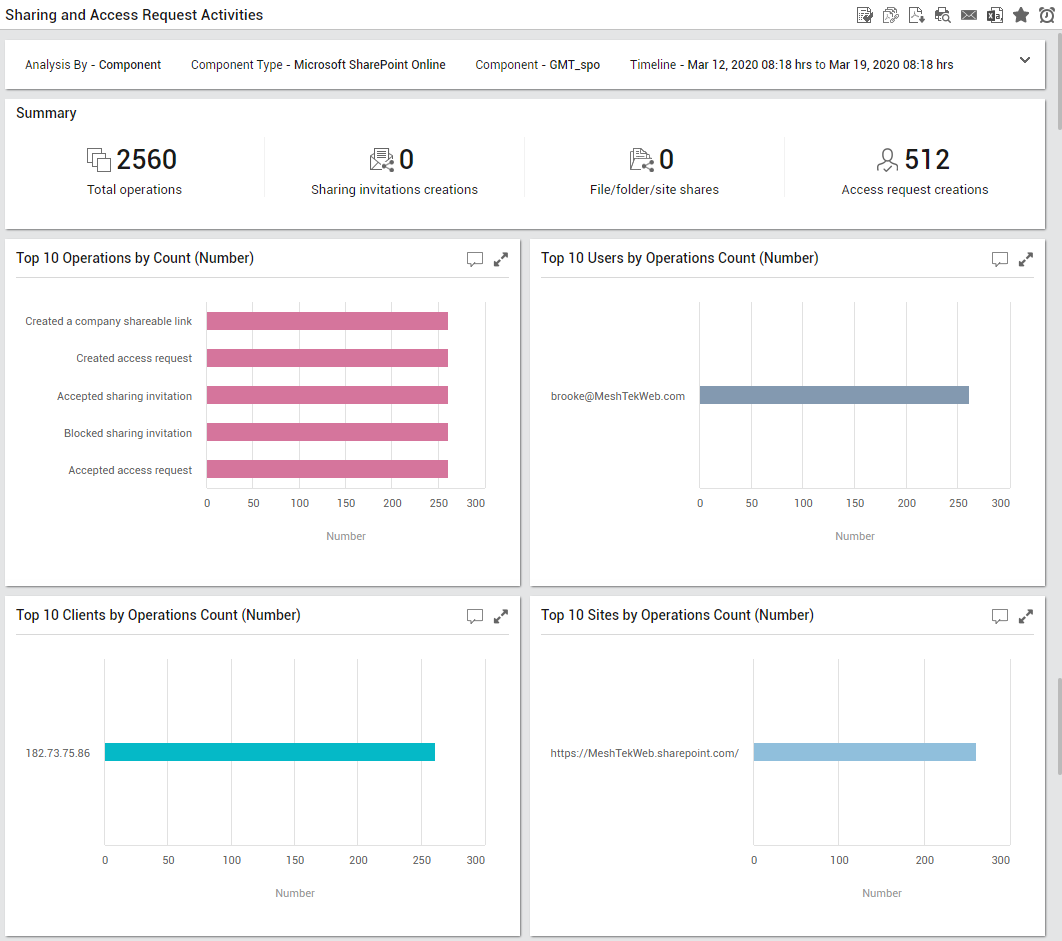
Figure 3 : The generated Sharing and Access Request Activities Report
-
The generated report (see Figure 3) contains the following sections:
- The Summary section provides an at-a-glance view of the number of access request and sharing-related operations that were performed by users of SharePoint Online organization and the number of sharing invitations created. This section also reveals the number of files/folders/sites that were shared with other users and the number of access requests created.
- A series of bar graphs appearing below the Summary section (see Figure 3) reveals the top 10 administrative users performing operations and the top 10 unique access request and sharing-related operations that were performed on SharePoint Online over a period of time. The top 10 unique users who performed operations related to access requests and sharing is also revealed. The top 10 unique clients from which the users initiated the access requests and operations and the top 10 unique sites on which the access request and sharing-related operations were performed can also be ascertained with ease.
-
The Top 10 Unique Users by Operations section (see Figure 4) reveals the users who performed access request and/or sharing-related operations on SharePoint Online. For each user, the operations performed by that user, the number of times the operations were performed, and the client from which that user initiated the operations are revealed. This way, administrators can quickly figure out if any user has performed any unauthorized operation.
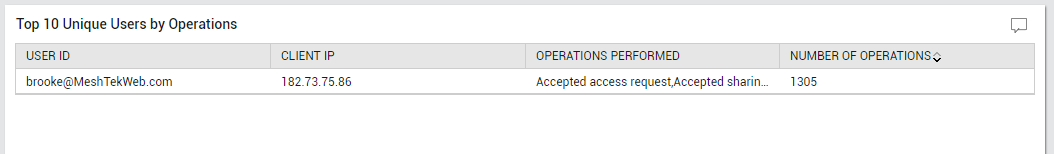
Figure 4 : The Top 10 Unique Users by Operations section in the generated report
-
The Top 10 Unique Destinations by Operations section (see Figure 5) reveals the destination URLs of the access request and sharing-related operations performed over a period of time. For each URL, the specific operations that resulted in that URL and the number of times the operations were performed are reported.
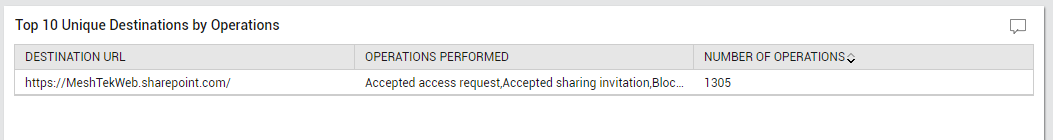
Figure 5 : The Top 10 Unique Destinations by Operations section in the generated report
-
The Top 10 Unique User Agent by Operations section (see Figure 6) lists the user-agent strings of browsers used by users for performing the access request and/or sharing-related operations. For each user-agent string, this section further reveals the number of operations performed using that browser. This will help administrators to identify the browser that was used most often to perform such operations.
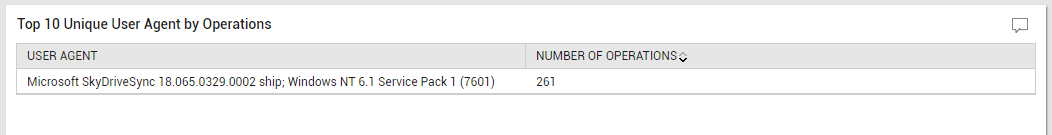
Figure 6 : The Top 10 Unique User Agent by Operations section in the generated report
-
To know which type of items - i.e., whether a file/folder/web/site/tenant/document library- was the target of the maximum number of access request and/or sharing-related operations in the chosen time period, use the Top 10 Affected Item Types by Operations section (see Figure 7). For each item type, this section reveals the specific operations performed on that type and the number of times the operations were performed.

Figure 7 : The Top 10 Affected Item Types by Operations section in the generated report
-
The Sharing and Access Request Operations Details section (see Figure 8) provides the exact count of sharing and access related operations performed for each category in the chosen time period. This will help administrators figure out the type of operation that was performed more frequently.
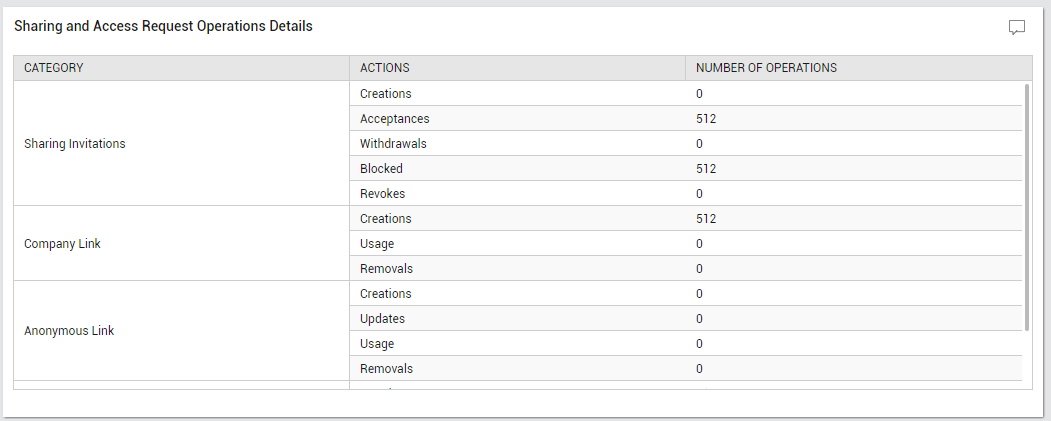
Figure 8 : The Sharing and Access Request Operation Details section in the generated report